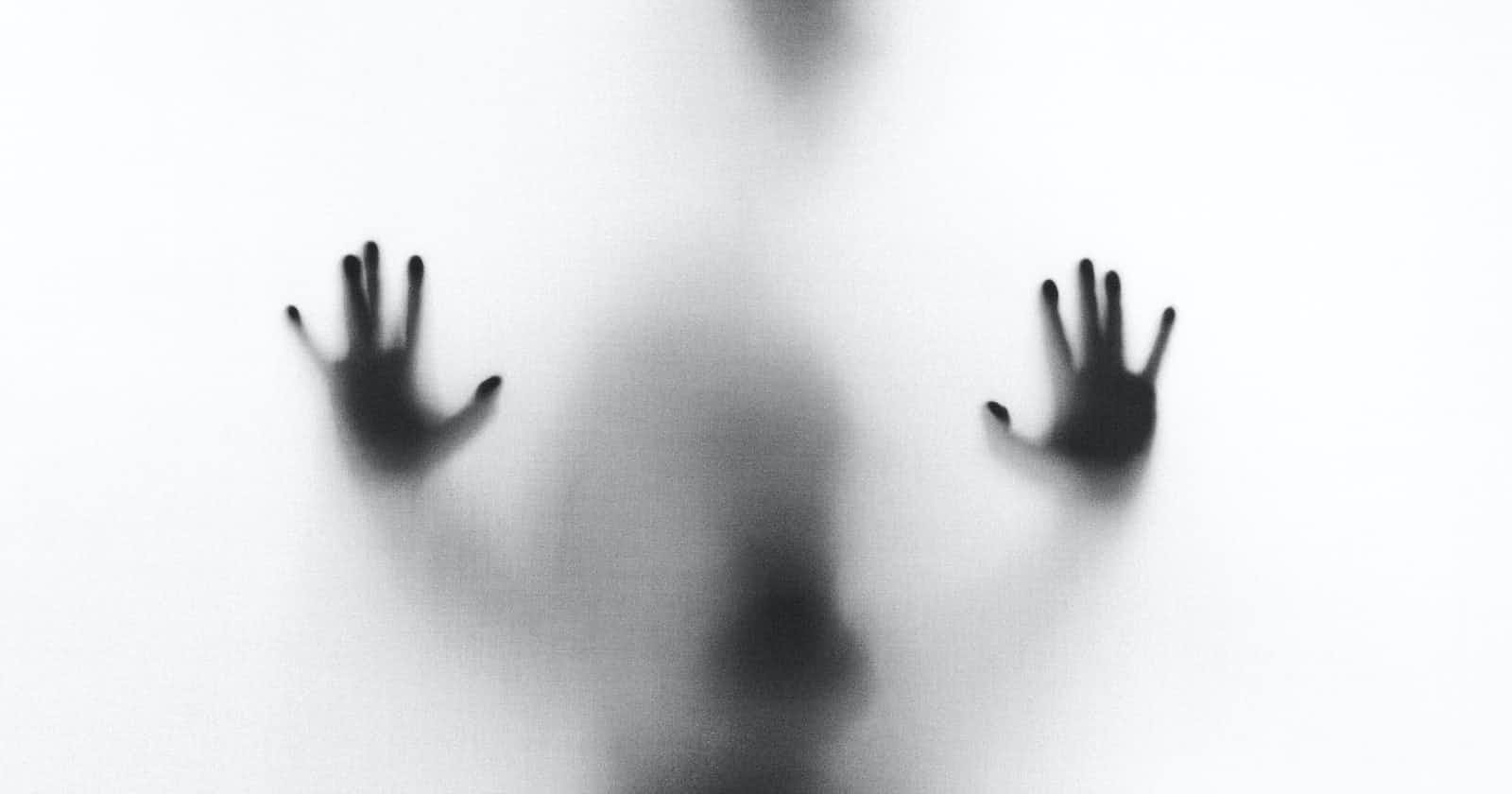
'Shadow IT' refers to everything IT that is invisible to IT department.
Dropbox, Trello, Slack, cloud office services from Google and Microsoft, all sorts of project and team management products, you name it. The shadow IT emerged within the easy-to-use and accessible SaaS business products trend. It has enabled business functions to directly use, and pay for IT services, often without permission and control of business governing bodies.
In the early days of digitalization, this might have looked like a progressive move. Indeed, why not encourage high digital literacy and self-sustained development within business departments. However, in this scenario, the IT department merely remained an infrastructure maintainer rather than a strategic business enabler.
Several factors make shadow IT dangerous for an organization aiming for digital leadership.
First being the duplication of efforts. IT service management (ITSM) best practices suggest that an organization should avoid having multiple business processes aiming at the same goal. Centralized and coordinated backups, identity and access rights management, or end-user support are hardly possible if business teams use different cloud services for the same purposes.
The second is 'siloing'. When data is 'siloed', it stays with the data creators and remains unavailable to anyone else in the organization. Effective companies aiming for value co-creation try to eliminate barriers to information flow within the organization. Meanwhile, shadow IT is one of the main obstacles in this way. The data generated and stored in 'shadowed' SaaS usually remains outside of the visibility of those not using the same service. Alternatively, siloed data gets exported and shared via filesharing, emails, and messengers, creating a mess with version control and access restriction.
The third major negative impact is the diminishing authority of the CIO. When a business utilizes the IT department only as a maintenance team for the internet and hardware, IT leadership will not have much weight in the strategic decision-making process.
The capability of IT to bring value to the business relies on the ability to influence and support strategic business agenda and provide a highly efficient and reliable set of value-added services. The existence and propagation of shadow IT take power away from the CIO and force IT back into the role of supportive function.
Cybersecurity is even more stringent about shadow IT as it jeopardizes the main principles of effective information access management and policy enforcement. First of all, shadow IT exists mostly inside SaaS. Which is the trickiest form of cloud setup to handle from the security perspective. Let alone establish the security baselines and enable policy adoption.
While most clouds are secure on the platform level, it does not mean it's impossible to circumvent this security by improper use. Rapid online research reveals many cases when sensitive data (PII included) published on Google/Microsoft SaaS platforms became exposed due to the wrong access settings. Open APIs, lax password standards, shared/abandoned/service accounts, etc., are common attributes of shadow IT.
Information asset inventory, the base for any subsequent risk management effort, is impossible if the information is scattered and hidden on the plethora of cloud services.
Business continuity planning is also tricky with SaaS. Unlike most B2B agreements, which define a particular service level agreement (SLA) and indemnity clauses, department or team-level SaaS subscriptions are usually provided on abest-effort basis.
Does it mean that shadow IT must be forbidden and eliminated? The coercive response is seldom an optimal answer.
Chances are, shadow IT has appeared for a reason. Most probably due to the poor execution or complexity of communication with the IT and cybersecurity departments. Probably end-users or data owners couldn't get the technology and performance needed to do the job, or information security gets in the way too much. In that case, users start trying to bypass the limitations quickly rather than engage in unpleasant negotiations.
The business functions are seldom willing to give away the comfort and autonomy of shadow IT, making key stakeholder management ever so important. For both CISO and CIO, it is essential to educate the board and executives about the risks and opportunity costs the organization is paying by not running IT in a centralized and coordinated way. Finally, IT must speak the business language and aim for top-down support.